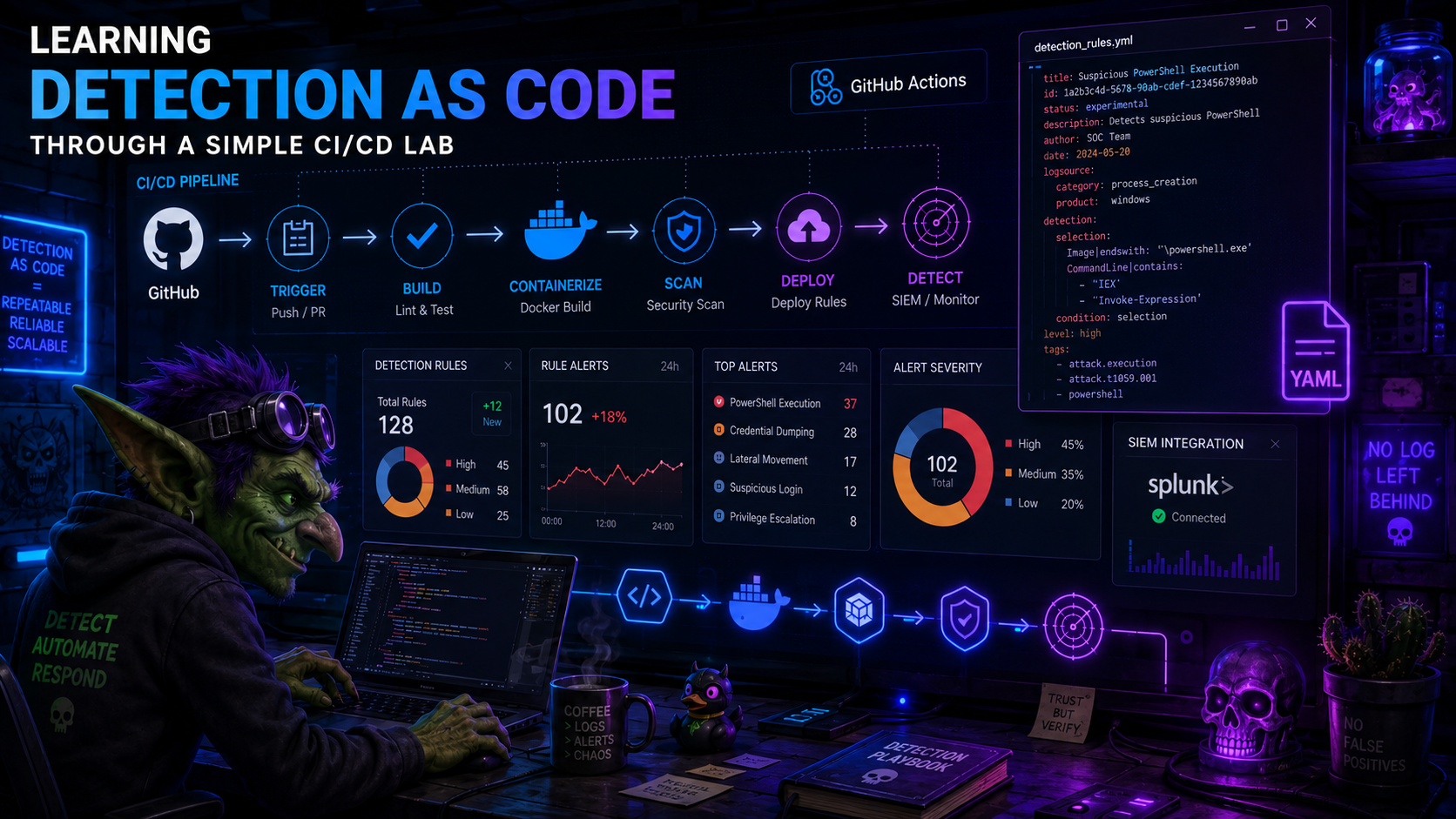
Learning Detection as Code Through a Simple CI/CD Lab
A practical lab note about building a small Detection as Code workflow with YAML detections, GitHub Actions, a self-hosted runner, and Splunk.
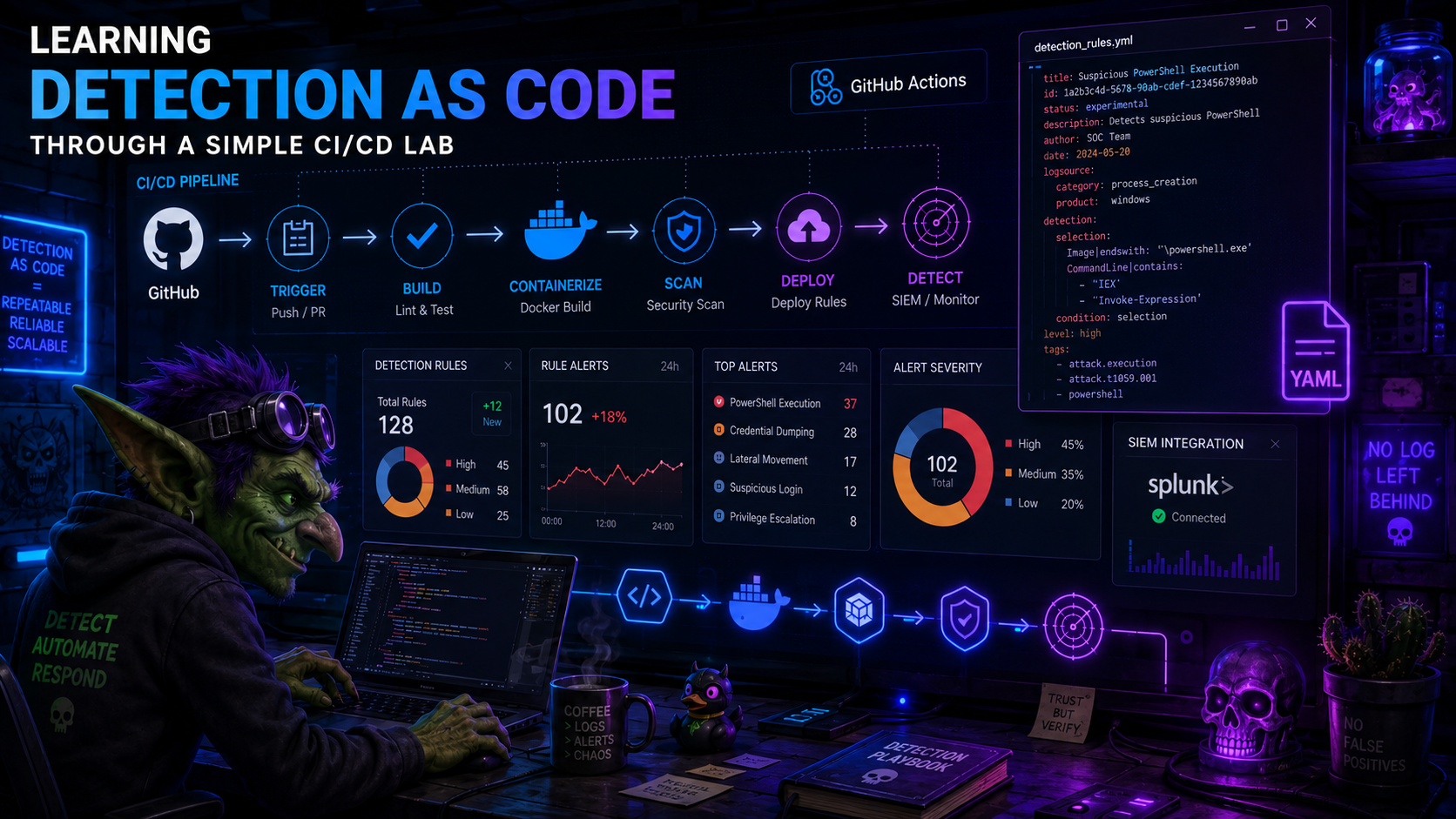
A practical lab note about building a small Detection as Code workflow with YAML detections, GitHub Actions, a self-hosted runner, and Splunk.

Transparency Note This post is based on my personal notes and lab practice from four learning tracks: Practical Threat Hunting (course), TH-200 (training), eCTHPv2 (certification path), and Cyber ...

A practical reflection on managing information overload in cybersecurity: from building a structured catalog of security RSS feeds to generating a daily, operationally focused SOC morning briefing that turns external news into actionable priorities.

Last year, I completed the TH-200: Foundational Threat Hunting course and the corresponding OSTH certification exam. I originally wrote my notes about a week after receiving my exam results. Rather...

I have been working in Information Security for several years. Between investigations, training sessions, studies, labs, and certifications, I realized that I learn best when I organize my ideas — ...